Several manuals and automated techniques and procedures are utilised to evaluate and rank security vulnerabilities in a system. A VA may attack servers or other underpinning infrastructure, apps, or both. Additionally, conducting a VA aids in determining the environment's security posture and the degree of threat exposure. VA can discover vulnerabilities by selecting if the system has the appropriate controls as intended to be deployed.



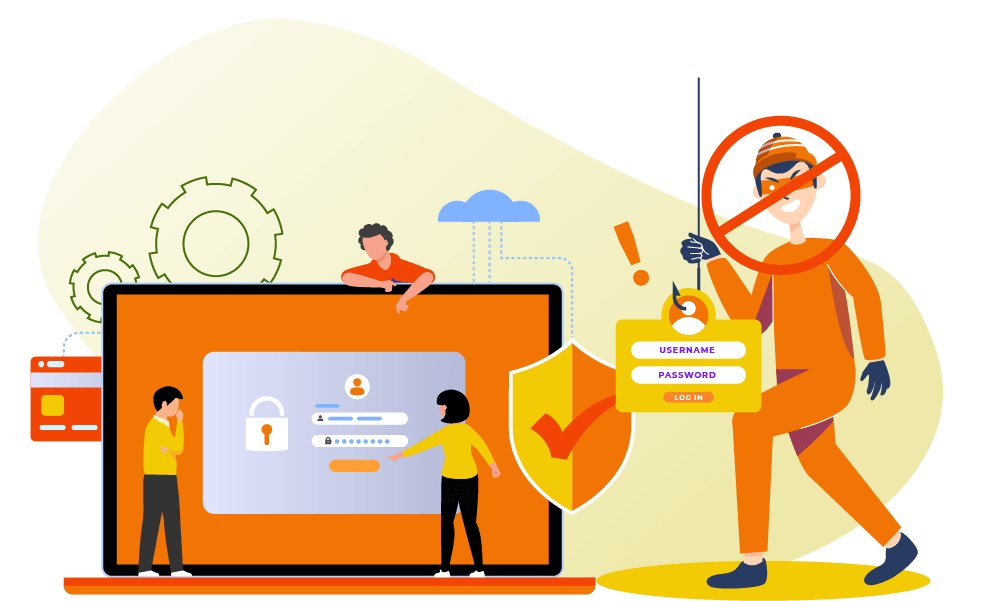
 Login
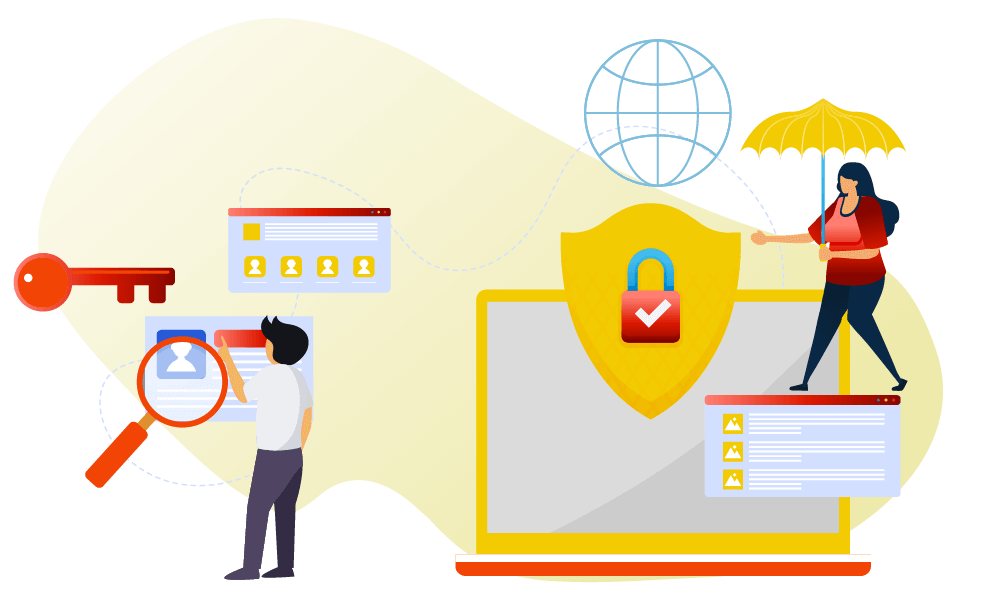
Login